2026.06.02
Breaking change! - This release contains API breaking changes. Please read the following release notes before upgrading.
Global Announcements
Admins can now send announcements to users through in-app notifications, email, or both. Recipients can be targeted in several ways:
- You can send announcements to Clients, Researchers (including admins), or both.
- When your selection includes clients, you can pick which client companies to notify.
- You can send announcements to users who are currently logged in, users who were active since a given timestamp, or all users.
- You can send announcements using in-app notifications, email, or both.
- You can set announcements to expire after a certain time (in-app only).
You can access this feature in Settings > Make Announcement, from the API (see the API documentation) or from the command line (useful for system administrators without Reporter accounts to announce downtime, for example).
Single Sign-On: SAML2 IdP-initiated SSO
Reporter now supports SAML2 Identity Provider-initiated SSO in addition to the existing Service Provider-initiated flow. If enabled, users can launch Reporter directly from their identity provider's dashboard (e.g. Azure AD, Okta, Google Workspace) without first navigating to the Reporter login page.
Enabling IdP-initiated SSO comes with security risks. See Documentation > General > Deployment > Configuration > Authentication > Methods > SAML2 Single Sign-On for more details.
Manage API tokens through the API
Listing, inspecting, creating, and deleting API tokens can now be done through the API itself, plus a new GET /api/v1/api-tokens/me endpoint lets a token look up its own details without any special abilities. Admins can also create tokens on behalf of other users.
Together with the scoped API tokens introduced in the previous release, this makes it much easier to automate tasks like provisioning dashboards or per-client integrations: a script can mint a short-lived token scoped to a single client or assessment on demand, rather than relying on a single, broadly permissioned token stored in a configuration file.
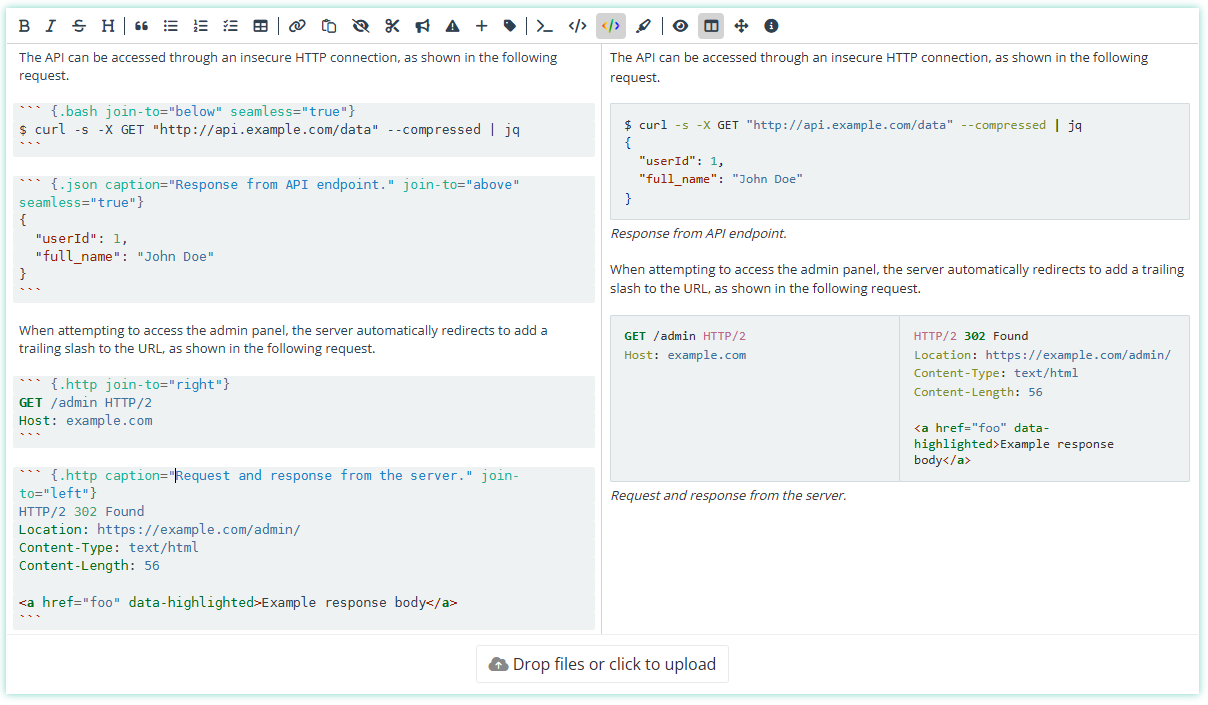
Horizontal rules
Added support for horizontal rules in markdown fields. The rule can be customized in color and width in Settings > Report Themes.
API breaking changes
Breaking change! - This release contains fixes and improvements to the API related to working with translatable models, such as finding and assessment templates. Some broken filters were removed and inconsistencies between list and search routes have been reduced. If you are using language functionality in your API scripts, you may be affected by the following breaking changes.
For all translatable models (finding template, assessment template, assessment section template, custom field, theme, and report page), the list routes (GET /{name of model}) have the following changes:
- Filtering by language now only narrows the result set; it no longer translates the results. The translating behavior was previously advertised in the docs but only ever worked on finding templates.
filter[language_id]has been renamed tofilter[language_ids], and a newfilter[and_language_ids]is available for matching records translated into multiple given languages.- To translate results, pass
?language_id=or?prefer_language=as a query parameter (unchanged).
Scripts using the /finding-templates/search route are also affected:
- Filter parameters have moved under
filter[...]to match list routes. For example, the filter query parameter?source=was changed to?filter[source]=. ?language_id=no longer narrows the result set. To narrow to templates that have a translation in a given language, use?filter[language_ids]=(or?filter[and_language_ids]=to require translations in multiple languages).?language_id=continues to select which translation fields are searched and used for rendering.- Scripts that previously relied on
?language_id=for ranking-boost (templates with a translation in that language ranked higher) should pass?prefer_language=as well to keep that behavior.
Improvements
- Researchers can now see the available assessment templates and their contents
- Keyboard shortcuts for mark tags and callouts now select the first option in the list
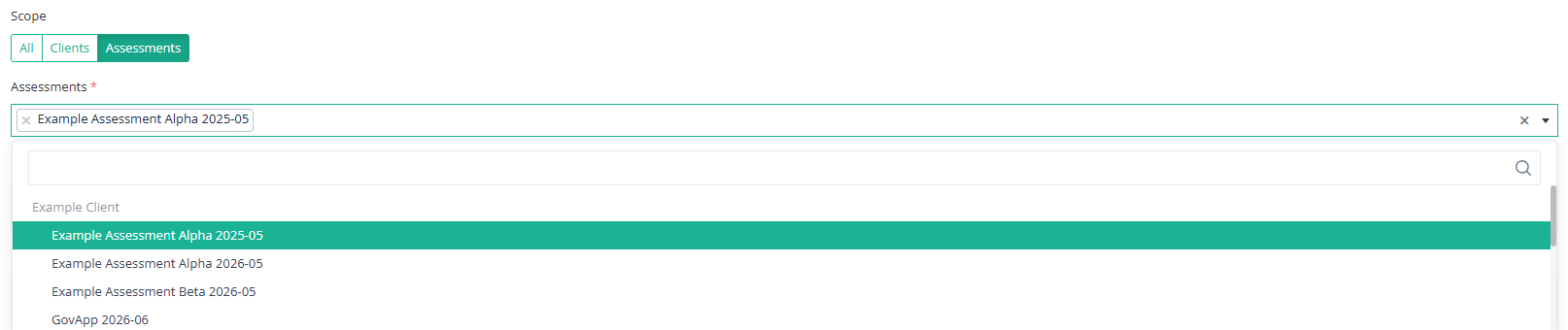
- Analytics, findings, and assessments can now be filtered by client tags and assessment tags
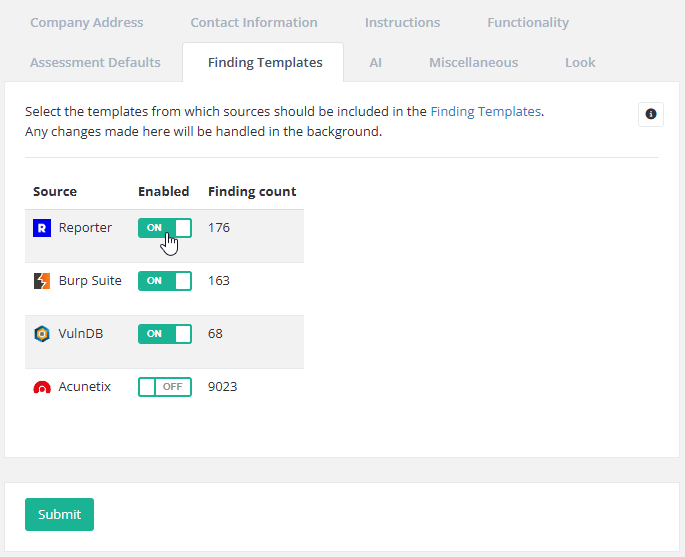
- Updated the parsers for tool findings and added 9 new parsers
- Parsers now import tags for tool findings and tool findings can be filtered by tag
Bug Fixes
- Fixed a bug that caused password setup links to be valid for 72 minutes instead of 72 hours.
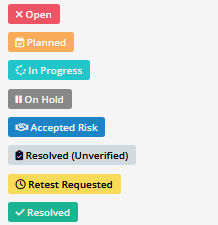
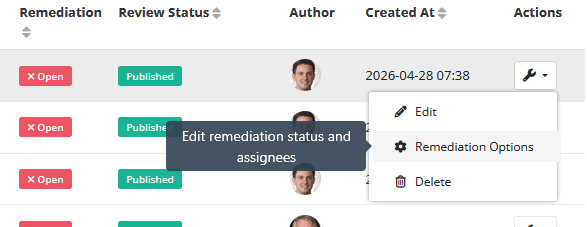
- Fixed an issue sending emails about changes to remediation status.
- Fixed an error when you unpublish and then republish a finding with at least one resolved target.
- Unpublished findings now always show up in the results table and checklist table components in draft PDF reports.
- Fixed a display issue in the results table caused by missing findings.
- Tasks to remove todo tags from findings now link to the finding.
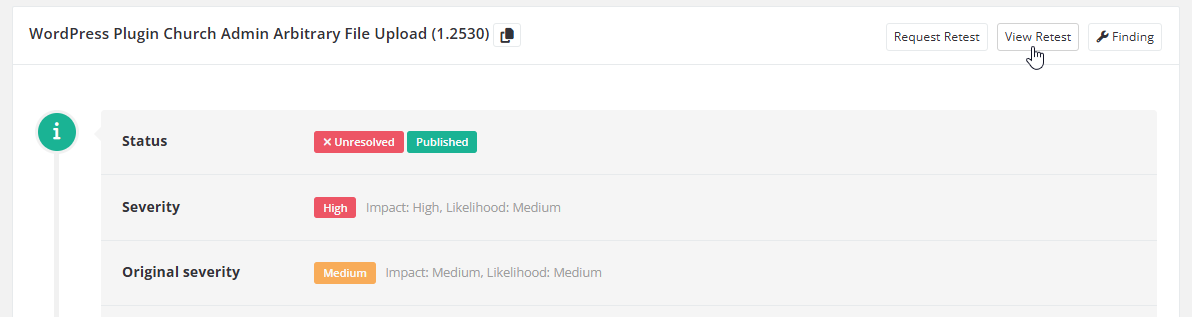
- Fixed an issue where draft report compilation would crash with unpublished retests.
- Files uploaded through the MCP server now have a name.
- Fixed a bug where researchers could see (but not use) the "publish" toggle when editing a finding.
- Fixed a bug in the grouped email logic that would only cause older notifications to be sent even if newer ones existed.